|
|
Home | Switchboard | Unix Administration | Red Hat | TCP/IP Networks | Neoliberalism | Toxic Managers |
| (slightly skeptical) Educational society promoting "Back to basics" movement against IT overcomplexity and bastardization of classic Unix | |||||||
Here are daemons that are "on" in a typical RHEL 5 installation:
# chkconfig --list | grep ':on' acpid 0:off 1:off 2:on 3:on 4:on 5:on 6:off anacron 0:off 1:off 2:on 3:on 4:on 5:on 6:off atd 0:off 1:off 2:off 3:on 4:on 5:on 6:off auditd 0:off 1:off 2:on 3:on 4:on 5:on 6:off autofs 0:off 1:off 2:off 3:on 4:on 5:on 6:off cpuspeed 0:off 1:on 2:on 3:on 4:on 5:on 6:off crond 0:off 1:off 2:on 3:on 4:on 5:on 6:off firstboot 0:off 1:off 2:off 3:on 4:off 5:on 6:off gpm 0:off 1:off 2:on 3:on 4:on 5:on 6:off haldaemon 0:off 1:off 2:off 3:on 4:on 5:on 6:off irqbalance 0:off 1:off 2:on 3:on 4:on 5:on 6:off jexec 0:on 1:on 2:on 3:on 4:on 5:on 6:on kudzu 0:off 1:off 2:off 3:on 4:on 5:on 6:off lm_sensors 0:off 1:off 2:on 3:on 4:on 5:on 6:off lvm2-monitor 0:off 1:on 2:on 3:on 4:on 5:on 6:off mcstrans 0:off 1:off 2:on 3:on 4:on 5:on 6:off mdmonitor 0:off 1:off 2:on 3:on 4:on 5:on 6:off messagebus 0:off 1:off 2:off 3:on 4:on 5:on 6:off microcode_ctl 0:off 1:off 2:on 3:on 4:on 5:on 6:off netfs 0:off 1:off 2:off 3:on 4:on 5:on 6:off network 0:off 1:off 2:on 3:on 4:on 5:on 6:off nfslock 0:off 1:off 2:off 3:on 4:on 5:on 6:off portmap 0:off 1:off 2:off 3:on 4:on 5:on 6:off rawdevices 0:off 1:off 2:off 3:on 4:on 5:on 6:off readahead_early 0:off 1:off 2:on 3:on 4:on 5:on 6:off readahead_later 0:off 1:off 2:off 3:off 4:off 5:on 6:off rhnsd 0:off 1:off 2:on 3:on 4:on 5:on 6:off rpcgssd 0:off 1:off 2:off 3:on 4:on 5:on 6:off rpcidmapd 0:off 1:off 2:off 3:on 4:on 5:on 6:off sendmail 0:off 1:off 2:on 3:on 4:on 5:on 6:off smartd 0:off 1:off 2:on 3:on 4:on 5:on 6:off sshd 0:off 1:off 2:on 3:on 4:on 5:on 6:off syslog 0:off 1:off 2:on 3:on 4:on 5:on 6:off sysstat 0:off 1:off 2:on 3:on 4:off 5:on 6:off vsftpd 0:off 1:off 2:on 3:on 4:on 5:on 6:off xfs 0:off 1:off 2:on 3:on 4:on 5:on 6:off xinetd 0:off 1:off 2:off 3:on 4:on 5:on 6:off yum-updatesd 0:off 1:off 2:on 3:on 4:on 5:on 6:off
That's 38 daemons in the list above. That reminds me Windows. Many of those do not have man pages (lm_sensors, lvm2-monitor, mcstrans, messagebus, netfs, rpcgssd, rpcidmapd) so who any why is using them for ordinary sysadmin is unknown.
Here are daemons that are typically off in a RHEL installation (in the example below along with junk daemons like avahi-daemon includes SElinux and iptables/ip6tables ;-):
[0]root@lusytp08: # chkconfig --list | grep -v ':on'
NetworkManager 0:off 1:off 2:off 3:off 4:off 5:off 6:off
avahi-daemon 0:off 1:off 2:off 3:off 4:off 5:off 6:off
avahi-dnsconfd 0:off 1:off 2:off 3:off 4:off 5:off 6:off
capi 0:off 1:off 2:off 3:off 4:off 5:off 6:off
cups 0:off 1:off 2:off 3:off 4:off 5:off 6:off
dnsmasq 0:off 1:off 2:off 3:off 4:off 5:off 6:off
dovecot 0:off 1:off 2:off 3:off 4:off 5:off 6:off
ip6tables 0:off 1:off 2:off 3:off 4:off 5:off 6:off
ipmi 0:off 1:off 2:off 3:off 4:off 5:off 6:off
iptables 0:off 1:off 2:off 3:off 4:off 5:off 6:off
iscsi 0:off 1:off 2:off 3:off 4:off 5:off 6:off
iscsid 0:off 1:off 2:off 3:off 4:off 5:off 6:off
isdn 0:off 1:off 2:off 3:off 4:off 5:off 6:off
kdump 0:off 1:off 2:off 3:off 4:off 5:off 6:off
ktune 0:off 1:off 2:off 3:off 4:off 5:off 6:off
mdmpd 0:off 1:off 2:off 3:off 4:off 5:off 6:off
multipathd 0:off 1:off 2:off 3:off 4:off 5:off 6:off
netconsole 0:off 1:off 2:off 3:off 4:off 5:off 6:off
netplugd 0:off 1:off 2:off 3:off 4:off 5:off 6:off
nfs 0:off 1:off 2:off 3:off 4:off 5:off 6:off
ntpd 0:off 1:off 2:off 3:off 4:off 5:off 6:off
o2cb 0:off 1:off 2:off 3:off 4:off 5:off 6:off
ocfs2 0:off 1:off 2:off 3:off 4:off 5:off 6:off
oraclevalidated 0:off 1:off 2:off 3:off 4:off 5:off 6:off
pcscd 0:off 1:off 2:off 3:off 4:off 5:off 6:off
psacct 0:off 1:off 2:off 3:off 4:off 5:off 6:off
rdisc 0:off 1:off 2:off 3:off 4:off 5:off 6:off
restorecond 0:off 1:off 2:off 3:off 4:off 5:off 6:off
rpcsvcgssd 0:off 1:off 2:off 3:off 4:off 5:off 6:off
saslauthd 0:off 1:off 2:off 3:off 4:off 5:off 6:off
setroubleshoot 0:off 1:off 2:off 3:off 4:off 5:off 6:off
smb 0:off 1:off 2:off 3:off 4:off 5:off 6:off
snmpd 0:off 1:off 2:off 3:off 4:off 5:off 6:off
snmptrapd 0:off 1:off 2:off 3:off 4:off 5:off 6:off
spamassassin 0:off 1:off 2:off 3:off 4:off 5:off 6:off
svnserve 0:off 1:off 2:off 3:off 4:off 5:off 6:off
vncserver 0:off 1:off 2:off 3:off 4:off 5:off 6:off
wdaemon 0:off 1:off 2:off 3:off 4:off 5:off 6:off
winbind 0:off 1:off 2:off 3:off 4:off 5:off 6:off
wpa_supplicant 0:off 1:off 2:off 3:off 4:off 5:off 6:off
ypbind 0:off 1:off 2:off 3:off 4:off 5:off 6:off
xinetd based services:
chargen-dgram: off
chargen-stream: off
daytime-dgram: off
daytime-stream: off
discard-dgram: off
discard-stream: off
echo-dgram: off
echo-stream: off
omni: on
rmcp: off
rsync: off
tcpmux-server: off
telnet: on
tftp: off
time-dgram: off
time-stream: off
|
|
Switchboard | ||||
| Latest | |||||
| Past week | |||||
| Past month | |||||
Red Hat Customer Portal
What is messagebus service used for in Red Hat Enterprise Linux ?
(Updated 23 May 2011, 9:04 AM GMTOn servers, D-Bus is used by applications such as hald to communicate with libvirt, rhn_register, and yum-updatesd.
On desktops, GNOME and KDE use this extensively, and require this service to be enabled to function correctly.
This is an essential service, and should be enabled on boot. For further information on D-Bus, refer to http://www.freedesktop.org/wiki/Software/dbus
A Unix daemon is a program that runs in the "background," enabling you to do other work in the "foreground," and is independent of control from a terminal. Daemons can either be started by a process, such as a system startup script, where there is no controlling terminal, or by a user at a terminal without "tying up" that terminal as the daemon runs. But which daemons can you safely play with? Which should you leave running?An introduction to daemons
The real-world (i.e., non-computer) definition of "daemon" is either a spirit (an evil one) or an inner or private voice. It's interesting to note that each of the real-world definitions actually does apply to Unix daemon programs. Like mythological daemons, Unix daemon programs skulk around unseen in the background just as a daemon would. And daemons act like an inner voice in that they can run continuously and, like a conscience, can always be accessed. The word "daemon" is one of those cases of chicken and egg computer acronyms in search of a definition and supposedly is based on "Disk And Execution MONitor" program.
An introduction to services
The daemons referenced in /etc/init.d are configured to be run as Linux services. Services are programs that are started and stopped through the init scripts in the /etc/init.d directory. Many of these services are launched when the system is booted. The /sbin/service utility provides a consistent interface to executing the init scripts. The init scripts provide a consistent interface to managing a service by providing options that start, stop, restart, query status, and perform other actions on services. For example, the httpd service init script provides these options:
/sbin/service httpd Usage: httpd {start|stop|restart|condrestart|reload|status|fullstatus|graceful|help|configtest}You can view the current state of all services with this option to the service utility:
/sbin/service –status-all acpid (pid 2481) is running... anacron (pid 2647) is running... atd (pid 2657) is running... auditd (pid 2189) is running... ....Runlevel information for these services, that is, the settings for which system runlevel the service will be started at boot time, can be queried and modified with the chkconfig utility. For example, to query the current settings for the syslog service:
/sbin/chkconfig --list syslog syslog 0:off 1:off 2:on 3:on 4:on 5:on 6:offThis shows that that syslog service will be automatically started at boot-time for runlevels 2, 3, 4, and 5. To set the service to not start for runlevels 3 and 4 (not a good idea, by the way), you would use these options for the chkconfig utility:
/sbin/chkconfig –levels 34 syslog offThe /usr/bin/system-config-services utility provides a GUI interface that enables you to both query and modify the current state of a service, as well as its defined run levels. See Illustration 1.
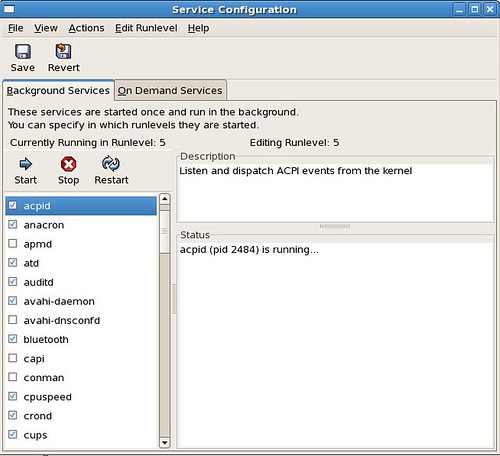
Illustration 1: The /usr/bin/system-config-services utility GUI
Let's look at how these services and daemons appear in output from ps. Here's a short list:
UID PID PPID C STIME TTY TIME CMD root 1 0 0 23:36 ? 00:00:00 init [5] root 2161 1 0 23:37 ? 00:00:00 auditd root 2177 1 0 23:37 ? 00:00:00 syslogd -m 0 root 2180 1 0 23:37 ? 00:00:00 klogd -x root 2207 1 0 23:37 ? 00:00:00 mcstransd root 2254 1 0 23:37 ? 00:00:00 rpc.statd root 2287 1 0 23:37 ? 00:00:00 rpc.idmapd root 2577 1 0 23:37 ? 00:00:00 crond root 2631 1 0 23:37 ? 00:00:00 /usr/sbin/atd root 2654 1 0 23:37 ? 00:00:00 rhnsd --interval 240What's important to note here? (Other than I'm staying up too late at night, that is.) For each of the daemons, the parent process ID (PPID) is 1. This indicates that the daemons were started up during the boot process by init.
A useful tool for viewing the "tree" of processes and their parents is "pstree." Here's a fragment of the output from pstree:
init-+ |-NetworkManager---2*[{NetworkManager}] |-NetworkManagerD |-acpid |-atd |-auditd-+-python | `-{auditd} |-avahi-daemon---avahi-daemon |-bonobo-activati---{bonobo-activati} |-crond |-cupsd---cups-polld |-2*[dbus-daemon---{dbus-daemon}] |-dbus-launch |-dhcdbd---dhclientA closer look at your system's daemons
So much for background information. Let's take a look at your system's daemons and see which ones you can safely play with. Note that for this article, the system used was running the Red Hat Enterprise Linux Beta 2 release, workstation configuration. Based on your specific system, you may see more or fewer daemons, or even some not included here.
We've listed web-sites where you can learn more about these daemons, but the best place to start learning is the manpage. O'Reilly also has an excellent alphabetic index of Linux commands and wikipedia.org has entries for most of these daemons. And, don't forget to look in the README files.
acpid
This is the daemon for the Advanced Configuration and Power Interface (ACPI). ACPI is an open industry standard for system control related actions, most notably plug-and-play hardware recognition and power management, such as startup and shutdown and putting systems into low poser consumption modes.
You'll probably never want to shut down this daemon, unless you are explicitly instructed to do so to debug a hardware problem.
Learn more:
http://www.acpi.infoanacron
One of the problems with living on a laptop, as so many of us do these days, is that when you set up a cron job to run, you can't always be sure that your laptop will be running at the time that the job should run. anacron (the name refers to its being an "anachronistic cron") gets around this problem by scheduling tasks in days. For example, anacron will run a job if the job has not been run in the specified number of days.
When are you safe not running anacron? When your system is running continuously. Should you simply stop cron from running if you have anacron running? No; anacron is able to specify job intervals in days, not hours and seconds.
Learn more:
http://anacron.sourceforge.netapmd
This is the daemon for the Advanced Power Management (APM) BIOS driver. The APM hardware standard and apmd are being replaced by ACPI and acpid. If your hardware supports ACPI, then you don't need to run apmd.
atd
This is the daemon for the at job processor (at enables you to run tasks at specified times). You can turn off this daemon if you don't use it.
autofs
This daemon automatically mounts disks and file systems that you define in a configuration file. Using this daemon can be more convenient that explicitly mounting removable disks.
Learn more:
http://freshmeat.net/projects/autofsauditd
The Linux Auditing System provides kernel-resident logging of system calls and user space tools to collect and view the logs. The auditd daemon writes the logging records to disk. auditd is configurable to allow control over what information is written to the logs.
Why should you keep auditd running? The information in the log may prove useful in debugging security-related issues. For example, auditd is used to log SELinux events. There are also utilities such as aureport that enable you to view the audit log. Here's an example of a report generated by aureport:
Summary Report ====================== Range of time in logs: 11/28/2006 06:07:04.800 - 02/06/2007 21:10:09.957 Selected time for report: 12/31/1969 19:00:00 - 02/06/2007 21:10:09.957 Number of changes in configuration: 285 Number of changes to accounts, groups, or roles: 32 Number of logins: 145 Number of failed logins: 11 Number of users: 2 Number of terminals: 22 Number of host names: 11 Number of executables: 27 Number of files: 91 Number of AVC denials: 688 Number of MAC events: 12 Number of failed syscalls: 404 Number of anomaly events: 0 Number of responses to anomaly events: 0 Number of crypto events: 0 Number of process IDs: 14022 Number of events: 70694Avahi-daemon and avahi-dnsconfd
The Avahi website defines Avahi as: 'a system which facilitates service discovery on a local network. This means that you can plug your laptop or computer into a network and instantly be able to view other people who you can chat with, find printers to print to, or find files being shared…' Avahi is a Zeroconf implementation. Zeroconf is an approach that enables users to create usable IP networks without having special configuration servers such as DNS servers.
A common use of the avahi-daemon is with Rhythmbox, so you can see music that is made available to be shared with others. If you're not sharing music or files on your system, you can turn off this daemon.Learn more:
http://avahi.org
http://zeroconf.orgBluetooth and hidd and pand
The name says it all. Run this service to enable your system to make use of Bluetooth devices. The name of the actual daemon is hcid (Host Controller Interface Daemon).
There's also a daemon named hidd. This is the Bluetooth Human Interface Device Daemon. It provides keyboard, mouse, and track-ball device support over Bluetooth.
And, there's pand. This daemon enables your computer to connect to ethernet networks using Bluetooth.
Learn more:
http://www.bluetooth.com
http://bluez.sourceforge.net/contrib/HOWTO-PANcapi
This daemon supports the Common ISDN Application Programming Interface. You'll run this if you're connecting to ISDN hardware components. The service runs capiinit.
Learn more:
http://www.capi.org/pagesconman
No, this isn't related to late-night infomercials about real estate investing. The conman service (and the conmand daemon) support console management. This supports multiple console devices and simultaneous users. It supports local serial devices and remote terminal servers (via the telnet protocol). If you're managing multiple servers, you may want to run conman.
Learn more:
http://home.gna.org/conman/cpuspeed
This daemon adjusts the CPU speed based on the power consumption. Less power is used when the CPU is idle, and more power is available when needed to improve performance. If you're running on a laptop, you might want to consider running cpuspeed.
Learn more:
http://carlthompson.net/Software/CPUSpeedcrond
This daemon automates the running of tasks. These jobs are necessary for any Linux or Unix system. Don't stop or disable this one.
Learn more:
http://www.unixgeeks.org/security/newbie/unix/cron-1.html
http://www.linuxhelp.net/guides/cron/CUPS and cups-config-daemon
This daemon is the "Common UNIX Printing Solution." Like the name implies, it's a printing system that can handle multiple data formats and printers. If you want to print, leave this daemon running.
Learn more:
http://www.cups.org
http://www.easysw.com/cups/index.phpdhcdbd
This is the DHcp Client D-Bus Daemon. According to The Free DeskTop wiki,
D-Bus is a message bus system, a simple way for applications to talk to one another. In addition to interprocess communication, D-Bus helps coordinate process lifecycle; it makes it simple and reliable to code a "single instance" application or daemon, and to launch applications and daemons on demand when their services are needed.
Do you want to run this daemon? If you're running your system on a network (and who isn't?), especially if you're moving between networks such as when you move from a wired network to wireless as you move around your office, then you should be running NetworkManager. (We'll discuss NetworkManager in a bit.)
The dhcdbd daemon provides a D-Bus interface to dhclient, the DHCP client from ISC. This makes it possible for NetworkManager can to query and control dhclient.
Learn more:
http://www.freedesktop.org/wiki/Software/dbusgpmd
This daemon enables you to use your mouse in text-based applications such as the Midnight Commander file manager and on the console. You might find this useful if you're working through situations in the console; otherwise, you'll be working in the X windowing system and you might never need gpmd.
hald
No, this isn't related to the evil computer in the film "2001, A Space Odyssey." In this context, HAL refers to the "Hardware Abstraction Layer." The HAL daemon collects this information about hardware devices from the kernel and the hardware and makes it available in a consistent manner.
Don't turn off this daemon. Multiple applications rely on it.
Learn more:
"Desktop and hardware configuration," by David Zeuthenhplipd
This daemon supports HP Linux Imaging and Printing (HPLIP) for printing, scanning, and faxing with HP inkjet and laser printers. HPLIP works CUPS by providing a backend to connect to HP devices.
Learn more:
http://hplip.sourceforge.nethsqldb
This is the daemon for a Java relational database. The daemon gets its name from the Hypersonic SQL project that has been discontinued. hsqldb is used widely in open source projects such as OpenOffice (it's the database behind the "base" feature) and is often used in demonstration programs, as it can run entirely in memory. It also runs fast. Should you run this daemon? Only if you have a specific program that makes use of it. But, it's a very useful tool, and if you're not familiar with it, it's worth taking a look.
Learn more:
http://hsqldb.org
http://dba.openoffice.orghttpd
The Apache web server. Used by almost 60% of all websites. If you want to host a website, you run Apache. Need we say more?
Learn more:
http://httpd.apache.orgip6tables and iptables
These daemons are firewalls. A firewall, according to Wikipedia, is an "information technology (IT) security device which is configured to permit, deny or proxy data connections set and configured by the organization's security policy. Firewalls can either be hardware and/or software based."
iptables functions by maintaining tables of IPv4 packet filter rules in the kernel. It checks incoming and outgoing packets against these rules and blocks packets that don't meet the rules. ip6tables does the same for IPv6 packets.
Which should you run? Both. Always. It's a dangerous world on the 'net.
Learn more:
http://www.netfilter.org
http://www.ipv6.orgirda
IrDA (Infrared Data Association) is an industry standard for inter-device wireless, infrared communications. Most laptops are configured with an IrDA infrared transceiver. You only need to run this daemon if you need to communicate via an infrared connection to other devices.
Learn more:
http://irda.sourceforge.netirqbalance
This daemon distributes hardware interrupts to the CPUs in SMP (symmetric processor: multi-processor architecture) systems to increase performance. The daemon balances savings in power consumption with performance.
You need not run this daemon on single processor systems, as it only has an effect on multiple-processor systems. Red Hat Kbase articles1 indicate that irqbalance is relevant on x86, x86_64, and AMD systems.
Learn more:
http://www.irqbalance.orgkudzu
This is a very useful daemon. At boot time, it detects if hardware devices have been added to or removed from the the system. It"s worthwhile to run kudzu at boot time, even if you don't plan on adding or removing hardware often. You might run into a situation where you add a device and just assume that the system will figure out that it's there. Also, since kudzu only runs at boot time, and does not stay running, there's no performance hit on the system.
Learn more:
http://fedora.redhat.com/projects/additional-projects/kudzulisa
This daemon gets its name from Lan Information Server. lisa provides a function similar to the MS-Windows Network Neighborhood and provides you access to servers, including CIFS (Common Internet File Systems) servers on your network. lisa only needs the TCP/IP stack to function. It sends ICMP echo requests to ranges of IP address that you define in its configuration file and waits for responses.
Learn more:
http://docs.kde.org/stable/en/kdenetwork/lisa
http://docs.kde.org/userguide/networking-with-windows.html
http://lisa-home.sourceforge.netlm_sensors
This daemon supports monitoring temperatures, voltages, and cooling fans. In order to make use of this daemon, your system hardware has to include sensors to perform this monitoring. You can only run this daemon if your hardware can support if. You probably don't want to run this daemon on a workstation. It's more likely to be used for hi-end, mission critical servers.
Learn more:
http://www.lm-sensors.org
http://freshmeat.net/projects/lm_sensorsmcstrans
SELinux Context Translation System Daemon. This daemon translates security context informartion into a human readable form. You can probably stop this daemon, but if you do, you'll see a change in the SELinux information displayed with ls -Z. For example, with the daemon running, you'll see:
ls -Z -rw-r--r-- jsmith jsmith user_u:object_r:user_home_t bookmarks.html drwxr-xr-x jsmith jsmith user_u:object_r:user_home_t Desktop -r-xr-xr-x jsmith jsmith user_u:object_r:user_home_t hello -r--r--r-- jsmith jsmith user_u:object_r:user_home_t hello.cAnd, with it stopped, you'll see:
ls -Z -rw-r--r-- jsmith jsmith user_u:object_r:user_home_t:s0 bookmarks.html drwxr-xr-x jsmith jsmith user_u:object_r:user_home_t:s0 Desktop -r-xr-xr-x jsmith jsmith user_u:object_r:user_home_t:s0 hello -r--r--r-- jsmith jsmith user_u:object_r:user_home_t:s0 hello.cNote that with the daemon stopped, the security context value of "s0" is displayed. mctrans translates this to a null display. Other security contexts are translated from alphanumeric values in their names.
Learn more:
http://fedoraproject.org/wiki/SELinux/Understanding
http://danwalsh.livejournal.commdmonitor and mdmpd
These two daemons are used with RAID (redundant array of inexpensive/independent disks) data storage systems. Mdmonitor starts, stops, and reloads the mdadm (multipath device monitoring and management) software RAID monitoring and management utilities. You should only run these daemons if you have RAID storage in your system.
Learn more:
http://www.linuxdevcenter.com/pub/a/linux/2002/12/05/RAID.htmlmessagebus
This is the D-BUS system-wide message bus daemon. This daemon broadcasts notifications of system events and such as changes in the printer queue or the adding and removing of devices. (Note that this is not the same operation as Kudzu, as it can take place while the system is running and not only at boot time.)
Learn more:
http://www.freedesktop.org/software/dbusnetplugd and ifplugd
These daemons configure Ethernet devices when cables are plugged in and deconfigure them when the cables are removes. Why would you want this to happen? It makes sense for laptops so that your network connections are only brought up when their cables are attached.
Note that the development of netplugd has been discontinued in favor of ifplugd.
Learn more:
http://0pointer.de/lennart/projects/ifplugdNetworkManager and NetworkManagerDispatcher
The NetworkManager daemon automates switching between network connections. This is a useful daemon for laptop users who switch between wireless WiFi connections and Ethernet connections. The NetworkManagerDispatcher daemon automatically runs scripts (including scripts to force any actions that you want to have happen such as setting up specific routes) when NetworkManager changes the network state.
Learn more:
http://www.gnome.org/projects/NetworkManagernamed
This daemon is the Domain Name Server. You'll need to run this daemon only if your system is acting as a DNS server for your network.
Learn more:
http://www.dns.net/dnsrdnfsd
The nfs daemon supports the nfs communications protocol for file sharing across TCP/IP networks. You'll want to run this daemon if you make use of file systems shared with nfs.
Learn more:
http://nfs.sourceforge.netnscd
This is the name service cache daemon. It takes care of group and password lookups for running programs and then caches the lookup results for the next query for services that can experience slowness in picking up changes such as NIS or LDAP. If you're running these services, you may want to run nscd.
ntpd
This is the Network Time Protocol daemon. This deamon sets and maintains the system time of day by keeping it in synch with Internet standard time servers. If your system is connected to the Internet (and who isn't?) then running ntpd will keep your system time correct.
Learn more:
http://www.ntp.orgoddjobd
The oddjobd daemon provides the com.redhat.oddjob service on the system-wide message bus. Each facility which oddjobd provides is provided as a separate D-Bus method. oddjobd provides support for unprivileged applications that require privileged operations to be performed.
You should only run this daemon if you are using an application that requires it, such as Conga.
Learn more:
http://people.redhat.com/nalin/oddjob/oddjob.html
http://sourceware.org/cluster/congaopenvpn
This daemon supports virtual private networks (VPNs). The daemon startup script says it all:
OpenVPN is a robust and highly flexible tunneling application that uses all of the encryption, authentication, and certification features of the OpenSSL library to securely tunnel IP networks over a single UDP port.
If your system is a node in a VPN, then you'll probably run OpenVPN.
Learn more:
http://openvpn.netpcscd
This is the PC/SC Smart Card Daemon. pcscd is the daemon for pcsc-lite (middleware for accessing smart cards) and the (java-based) MuscleCard framework. It enables communications with smart card readers and smart cards.
(A smart card is a card that is embedded with either a memory chip or microprocessor and a memory chip. And Muscle is the Movement for the Use of Smart Cards in a Linux Environment.)
Learn more:
http://www.smartcardalliance.org
http://pcsclite.alioth.debian.org
http://www.linuxnet.com/musclecard/index.htmlportmap
The portmapper daemon manages RPC (remote procedure call) connections. It converts RPC program numbers into TCP/IP (or UDP/IP) protocol port numbers. The most common use of portmapper is by NFS and NIS.
So, if your system relies on NIS or NFS, don't turn off the portmap daemon.
Learn more:
http://www.linux-nis.org/nis-howto/HOWTO/portmapper.htmlpostfix
This daemon is a mail transport agent. Unless your system is a mail relay server, you don't need to run this daemon.
Learn more:
http://www.postfix.orgrdisc
This daemon (the router discovery daemon) discovers routers on the local subnet. It is run at boot time to populate the network routing tables with default routes.
Learn more:
http://www.informit.com/articles/article.asp?p=23951&rl=1restorecond
This is an SELinux daemon. restorecond watches for file creation (of files listed in /etc/selinux/restorecond.conf) and then ensures that the files have the correct file context associated with the policy, and then sets the default SELinux file context.
Don't turn this one off. SELinux needs it.
Learn more:
http://fedoraproject.org/wiki/SELinux/Understanding
http://danwalsh.livejournal.com/rhnsd
This daemon periodically checks for actions that have been scheduled though the Red Hat Network web interface and runs them. This includes actions such as installing, removing, or updating software, rebooting the system, starting a kickstart installation, or installing configuration files.
Learn more:
https://www.redhat.com/rhn/rpcgssd and rpcidmapd and rpcsvcgssd
The rpcgssd and rpcsvcgssd daemons handle security for RPC. The rpcidmapd maps user names to UID and GID numbers.
If you're running NFS or NIS, then you should have these daemons running.
Learn more:
http://nfs.sourceforge.net/readahead_early and readahead_later
The readahead daemon causes the programs used during startup to be loaded into memory before they are needed, to improve startup performance.
saslauthd
This is the SASL authentication server daemon. SASL is the Simple Authentication and Security Layer and allows for adding authentication to connection-based protocols.
Learn more:
http://asg.web.cmu.edu/saslsendmail
This is a SMTP (Simple Mail Transfer Protocol) server. sendmail moves mail from one system to another as a Mail Transport Agent. If you run a mail program such as Thunderbird or Evolution, you don't need to run sendmail.
Learn more:
http://www.sendmail.orgsetroubleshoot
This is the SELinux Troubleshooting Daemon. setroubleshooter is one of the great recent additions to SELinux. setroubleshooter provides real-time feedback to users on SELInux AVC denials. And it provides this feedback in a easy to follow format.
Learn more:
https://hosted.fedoraproject.org/projects/setroubleshootsmartd
This daemon monitors the SMART (Self-Monitoring, Analysis and Reporting Technology) systems included in many types of disk drives, such as SCSI-3 type drives. The daemon will monitor reliability and performs self-tests. You should run this daemon if your hardware supports it.
Learn more:
http://sourceforge.net/projects/smartmontoolsspamassassin
This daemon uses the Apache SpamAssassin program to check email for SPAM. It is usually run on a mail deleivery agent (MDA) server. If you use a client program such as Thunderbird or Evolution to access your mail, then you don't need to run spamassassin.
Learn more:
http://spamassassin.apache.orgsshd
This is the daemon for open ssh. ssh replaces the insecure rsh and rlogin programs and enables encryption for communications between hosts over insecure networks. If you connect with other systems over the public Internet, you want to use ssh and run this daemon.
Learn more:
http://www.ssh.com
http://www.openssh.comsyslog
syslog is the standard logging system for Linux systems. Don't turn this one off.
Learn more:
http://www.syslog.orgwinbind
This daemon is part of the Samba suite and enables Windows domain users to function as Unix users on Unix servers. You may want to run this daemon if you're dealing with a mixed PC and Linux/Unix network.
Learn more:
http://www.samba.org/samba/docs/man/Samba-HOWTO-Collection/winbind.html
http://www.samba.orgxfs
This damon is the xfs font server. This daemon loads fonts into memory to enable X applications to run faster than if they had to load the fonts from disk. This daemon is worth running to improve application performance.
Learn more:
http://linuxreviews.org/howtos/xfree/xfsypbind
This daemon binds NIS clients to an NIS domian. The "yp" refers to "yellow pages," as the NIS directory of user accounts acts like the telephone book yellow pages. You only want to run this daemon if your system relies on NIS (Network Information Service) for user accounts and system names.
Learn more:
http://www.linux-nis.orgyum-updatesd
yum-updatesd checks for software updates and can send notifications of these updates via mail, dbus, or syslog messages, or can automatically install the updates. The dbus messages are picked up by the "puplet" (package updater), which notifies the user of the updates and lets the user install them.
Learn more:
http://linux.duke.edu/projects/yum
http://www.redhat.com/magazine/024oct06/features/fc62References
"Which Services Can I Disable?," Dinkar, Tejas
Linux Services, Devices, and Daemons
Fedora Core 3 Linux Services
Services in Fedora, Mauriat MirandaAcknowledgments
I'd like to acknowledge the information presented by Mauriet Miranda in his "Services in Fedora" web-site. His work was especially helpful as a starting point for researching this article. Also, I'd like to thank Christopher Smith, James Bowes, and Dan Walsh for their insightful technical information in writing the article.
Len DiMaggio is a QE Engineer at Red Hat in Westford, Massachusettes and has published articles on software engineering in Red Hat Magazine, Dr. Dobbs Journal, Software Development Magazine, IBM Developerworks, STQE, and other journals.
This entry was posted by Len DiMaggio on Friday, March 9th, 2007 at 6:17 am and is filed under Red Hat Enterprise Linux. You can follow any responses to this entry through the RSS 2.0 feed. Both comments and pings are currently closed.
16 responses to "Understanding your (Red Hat Enterprise Linux) daemons"
- Ben Russo says:
March 9th, 2007 at 11:18 amHow about adding a "service XXX help" init script command option that would give a description of the service and give examples of what types of servers should have it running, and what types of servers could turn it off. It could just look under /usr/share/doc/services/XXX for a file. each RPM that installs a file in /etc/init.d would drop a corresponding description in /usr/share/doc/services/
Thanks!
-Ben.- Ashish Malik says:
March 10th, 2007 at 1:10 amThe article was great…:) It's difficult to find such type of info about all the services at one place. Finally, RedHat did it. It's a good tutorial for beginners.
But I am not bale to find about "service httpd condrestart". What does this condrestart does?
- Len DiMaggio says:
March 10th, 2007 at 2:14 pmHi Ashish – thanks for the kind comment – here's a fragment from the httpd startup script – the "condrestart" is a conditional restart. it only restarts the service if it's running, unlike restart, which always restarts the service.
==================================
restart)
stop
start
;;
condrestart)
if [ -f ${pidfile} ] ; then
stop
start
fi
;;
==================================- Jovonnie Chesney says:
March 13th, 2007 at 3:28 amI agree with Ashish-this is an excellent and well written! Len, thank you for consolidating information from multiple sources into a single, easy to digest article that is both practical and a great study resource.
- Wolf says:
March 14th, 2007 at 3:26 pm/sbin/service –status-all should be /sbin/service -–status-all
- hermouche says:
March 18th, 2007 at 8:36 pmGreat job.
Agree with Wolf.
thanks- Len DiMaggio says:
March 19th, 2007 at 1:50 amWolf is correct – the syntax is: /sbin/service -–status-all
Good catch!
- Swapnil says:
March 21st, 2007 at 11:27 pmThanks a lot for this article.
I was looking for this for quite some time.- Dean Gibson says:
April 4th, 2007 at 2:39 pmI don't agree that "If you run a mail program such as Thunderbird or Evolution, you don't need to run sendmail." The two programs perform different tasks.
If your system generates mail messages (eg, the daily logwatch), then you probably need to run sendmail or postfix.
- Fred New says:
April 5th, 2007 at 2:23 amThis is a useful list of services. Well done. If this isn't already available in the online Red Hat documentation, it would probably find more readers there. It would also be useful to know how to configure IP tables ports for various services, like for CUPS, NFS and Samba. And speaking of Samba, maybe nmb and smb should be in this list.
- Vladimir says:
April 10th, 2007 at 10:01 pmIt's a good tutorial for beginners
Best Regards!- Patrick Wolfe says:
September 9th, 2007 at 10:45 amrpcgssd, rpcsvcgssd and rpcidmapd are only used by version 4 of the NFS protocol. Since most NFS clients use version 3, not version 4, these daemons are quite often safe to disable.
The easy way to tell which version you use is by checking your /etc/fstab and /etc/auto.* files. If you use the fstype "nfs", you're using protocol version 3. If you see "nfs4″, then you're using protocol version 4, and require these daemons.
- http film says:
February 1st, 2008 at 3:55 pmhttp film
cool site
- Vitaly says:
March 31st, 2008 at 4:40 amRegarding HAL daemon – is it used only by "desktop" application? I.e., may I stop hald for runlevel 3?
- Tux Training " Blog Archive " A step-by-step guide to building a new SELinux policy module says:
May 12th, 2008 at 4:46 pm[...] Since simple daemon applications usually have security goals close to what the application is designed to do,a good place to begin writing policy is for daemons started during the system startup routines or CGI scripts. Avoid writing policy for user applications until you thoroughly understand SELinux and your security goals for that application. [...]
- Amr Hamdy says:
January 28th, 2009 at 7:32 pmThanks a lot,
Very useful article … It's the only article I found to mention the real need or no-need to run mcstrans service
Society
Groupthink : Two Party System as Polyarchy : Corruption of Regulators : Bureaucracies : Understanding Micromanagers and Control Freaks : Toxic Managers : Harvard Mafia : Diplomatic Communication : Surviving a Bad Performance Review : Insufficient Retirement Funds as Immanent Problem of Neoliberal Regime : PseudoScience : Who Rules America : Neoliberalism : The Iron Law of Oligarchy : Libertarian Philosophy
Quotes
War and Peace : Skeptical Finance : John Kenneth Galbraith :Talleyrand : Oscar Wilde : Otto Von Bismarck : Keynes : George Carlin : Skeptics : Propaganda : SE quotes : Language Design and Programming Quotes : Random IT-related quotes : Somerset Maugham : Marcus Aurelius : Kurt Vonnegut : Eric Hoffer : Winston Churchill : Napoleon Bonaparte : Ambrose Bierce : Bernard Shaw : Mark Twain Quotes
Bulletin:
Vol 25, No.12 (December, 2013) Rational Fools vs. Efficient Crooks The efficient markets hypothesis : Political Skeptic Bulletin, 2013 : Unemployment Bulletin, 2010 : Vol 23, No.10 (October, 2011) An observation about corporate security departments : Slightly Skeptical Euromaydan Chronicles, June 2014 : Greenspan legacy bulletin, 2008 : Vol 25, No.10 (October, 2013) Cryptolocker Trojan (Win32/Crilock.A) : Vol 25, No.08 (August, 2013) Cloud providers as intelligence collection hubs : Financial Humor Bulletin, 2010 : Inequality Bulletin, 2009 : Financial Humor Bulletin, 2008 : Copyleft Problems Bulletin, 2004 : Financial Humor Bulletin, 2011 : Energy Bulletin, 2010 : Malware Protection Bulletin, 2010 : Vol 26, No.1 (January, 2013) Object-Oriented Cult : Political Skeptic Bulletin, 2011 : Vol 23, No.11 (November, 2011) Softpanorama classification of sysadmin horror stories : Vol 25, No.05 (May, 2013) Corporate bullshit as a communication method : Vol 25, No.06 (June, 2013) A Note on the Relationship of Brooks Law and Conway Law
History:
Fifty glorious years (1950-2000): the triumph of the US computer engineering : Donald Knuth : TAoCP and its Influence of Computer Science : Richard Stallman : Linus Torvalds : Larry Wall : John K. Ousterhout : CTSS : Multix OS Unix History : Unix shell history : VI editor : History of pipes concept : Solaris : MS DOS : Programming Languages History : PL/1 : Simula 67 : C : History of GCC development : Scripting Languages : Perl history : OS History : Mail : DNS : SSH : CPU Instruction Sets : SPARC systems 1987-2006 : Norton Commander : Norton Utilities : Norton Ghost : Frontpage history : Malware Defense History : GNU Screen : OSS early history
Classic books:
The Peter Principle : Parkinson Law : 1984 : The Mythical Man-Month : How to Solve It by George Polya : The Art of Computer Programming : The Elements of Programming Style : The Unix Hater’s Handbook : The Jargon file : The True Believer : Programming Pearls : The Good Soldier Svejk : The Power Elite
Most popular humor pages:
Manifest of the Softpanorama IT Slacker Society : Ten Commandments of the IT Slackers Society : Computer Humor Collection : BSD Logo Story : The Cuckoo's Egg : IT Slang : C++ Humor : ARE YOU A BBS ADDICT? : The Perl Purity Test : Object oriented programmers of all nations : Financial Humor : Financial Humor Bulletin, 2008 : Financial Humor Bulletin, 2010 : The Most Comprehensive Collection of Editor-related Humor : Programming Language Humor : Goldman Sachs related humor : Greenspan humor : C Humor : Scripting Humor : Real Programmers Humor : Web Humor : GPL-related Humor : OFM Humor : Politically Incorrect Humor : IDS Humor : "Linux Sucks" Humor : Russian Musical Humor : Best Russian Programmer Humor : Microsoft plans to buy Catholic Church : Richard Stallman Related Humor : Admin Humor : Perl-related Humor : Linus Torvalds Related humor : PseudoScience Related Humor : Networking Humor : Shell Humor : Financial Humor Bulletin, 2011 : Financial Humor Bulletin, 2012 : Financial Humor Bulletin, 2013 : Java Humor : Software Engineering Humor : Sun Solaris Related Humor : Education Humor : IBM Humor : Assembler-related Humor : VIM Humor : Computer Viruses Humor : Bright tomorrow is rescheduled to a day after tomorrow : Classic Computer Humor
The Last but not Least Technology is dominated by two types of people: those who understand what they do not manage and those who manage what they do not understand ~Archibald Putt. Ph.D
Copyright © 1996-2021 by Softpanorama Society. www.softpanorama.org was initially created as a service to the (now defunct) UN Sustainable Development Networking Programme (SDNP) without any remuneration. This document is an industrial compilation designed and created exclusively for educational use and is distributed under the Softpanorama Content License. Original materials copyright belong to respective owners. Quotes are made for educational purposes only in compliance with the fair use doctrine.
FAIR USE NOTICE This site contains copyrighted material the use of which has not always been specifically authorized by the copyright owner. We are making such material available to advance understanding of computer science, IT technology, economic, scientific, and social issues. We believe this constitutes a 'fair use' of any such copyrighted material as provided by section 107 of the US Copyright Law according to which such material can be distributed without profit exclusively for research and educational purposes.
This is a Spartan WHYFF (We Help You For Free) site written by people for whom English is not a native language. Grammar and spelling errors should be expected. The site contain some broken links as it develops like a living tree...
|
|
You can use PayPal to to buy a cup of coffee for authors of this site |
Disclaimer:
The statements, views and opinions presented on this web page are those of the author (or referenced source) and are not endorsed by, nor do they necessarily reflect, the opinions of the Softpanorama society. We do not warrant the correctness of the information provided or its fitness for any purpose. The site uses AdSense so you need to be aware of Google privacy policy. You you do not want to be tracked by Google please disable Javascript for this site. This site is perfectly usable without Javascript.
Last modified: October 03, 2017